Holder is wrong - backdoors and security can not coexist.
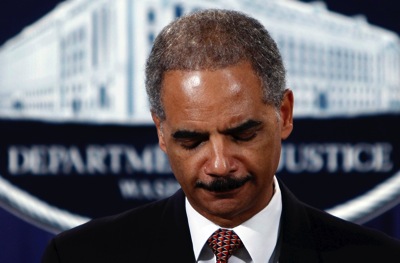 In the article below Attorney General Eric Holder said "“It is fully possible to permit law enforcement to do its job while still adequately protecting personal privacy”
In the article below Attorney General Eric Holder said "“It is fully possible to permit law enforcement to do its job while still adequately protecting personal privacy”
This is simply not true, and harkens back to the discredited arguments made by the FBI in the 1990’s about the Clipper Chip. It is hard enough to make secure computing systems, and we are not very good at it as all the breaches demonstrate. Intentionally introducing a vulnerability, which is the essential nature of back door or law enforcement access, is madness. If there is a back door, then keys exist, and can be compromised or reverse engineered. It is an added complexity to the system, which is almost certain to introduce other vulnerabilities. Its use would not be restricted to the US. Once it exists every government will demand access.
Social media and the cloud have tilted the balance of power absurdly towards law enforcement. This argument that they must retain access to encrypted cell phones is fatuous.
Holder urges tech companies to leave device backdoors open for police - The Washington Post
Lance Cottrell is the Founder and Chief Scientist of Anonymizer. Follow me on Facebook, Twitter, and Google+.