2 Apple security fumbles: Random MAC and Password Prediction
 Apple is getting taken to task for a couple of security issues.
Apple is getting taken to task for a couple of security issues.
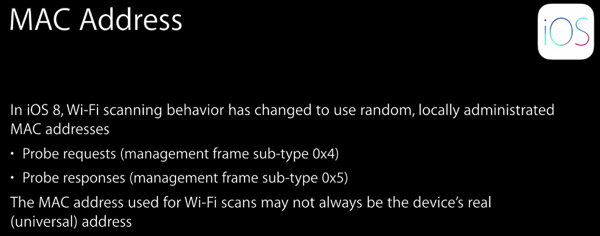
First, their recently announced “Random MAC address” feature does not appear to be as effective as expected. The idea is that the iOS 8 device will use randomly generated MAC addresses to ping WiFi base stations when it is not actively connected to a WiFi network. This allows your phone to identify known networks and to use WiFi for enhanced location information without revealing your identity or allowing you to be tracked. Unfortunately the MAC only changes when the phone is sleeping, which is really rare with all the push notifications happening all the time. The effect is that the “random” MAC addresses are changed relatively infrequently. The feature is still good, but needs some work to be actually very useful.
Second, people are noticing their passwords showing up in Apples iOS 8 predictive keyboard. The keyboard is designed to recognize phrases you type frequently so it can propose them to you as you type, thus speeding message entry. The problem is that passwords often follow user names, and may be typed frequently. Research is suggesting that the problem is from websites that fail to mark their password fields. Apple is smart enough to ignore text in known password fields, but if it does not know that it is a password, then the learning happens. It is not clear that this is Apple’s fault, but it is still a problem for users. Auto-fill using the latest version of 1Password should protect against this.
https://www.youtube.com/watch?v=ceC9jMIpszI
[powerpress]
Lance Cottrell is the Founder and Chief Scientist of Anonymizer. Follow me onFacebook, Twitter, and Google+.